Boost Your Online Privacy and Security with Advanced Tips
With social networks and tons of places to spend time online it is important to be aware of security measures you can take and what pitfalls to avoid. With the default stock configuration of your systems and browsers, you should be safe but whether you are safe enough depends on how seriously you take your safety and privacy online.
The need of the hour is to move beyond simple security measures and opt for advance techniques like data encryption and two-factor authentication etc. to have a safe, secure and private online experience. Here are some of safety measures you should know of and take heed, to make yourself safer online.
How You Are Helping Hackers Steal Your Data
Learn how to keep your online data safe with these tips and tricks. Protect your personal information from... Read more
Check for telltale signs
There are a few telltale signs that indicate a problem or something fishy with a site.

- Padlock icons: Green padlock is good but any other color (orange, yellow or red) indicates a issue.
- HTTPS in the address bar: HTTPS means the site is on a secure connection (and safe from prying eyes). By January 2017, Chrome will label HTTP connections as not secure.
- Phishing and malware alerts: Such alerts given by the browser means the site is insecure to visit and must not be viewed, in any case.
- Suspicious attachments in email: Emails with suspicious attachments are likely spam and may lead to phishing attacks
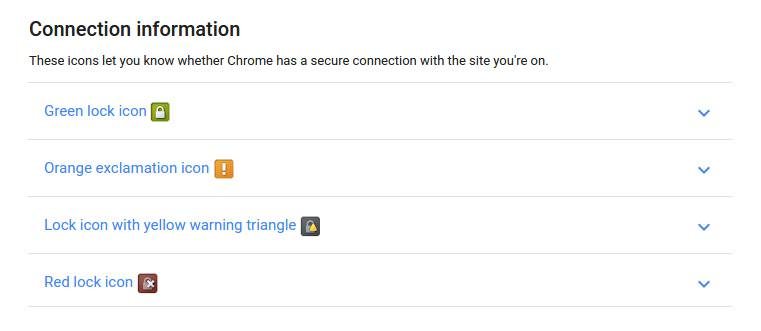
These are the indicators that the website or page you’re viewing is not safe/secure, known of having malware or exploited for malicious use like cheating people, hacking into their data, etc. There is also danger in the handling of payment details leading to potential thefts or other attacks.
Avoid sharing info with strangers (or new friends)
With the increasing use of social networks, we run the risk of oversharing what we shouldn’t. If we are not careful this could lead to identity theft issues or stalking cases.
If you are not familiar with privacy or security settings, here are a few tools and posts with tips you can use to configure privacy settings in popular social networks.
- Privacy Checkup
- Security Tips
- Privacy Basics
- 5 Facebook Privacy Settings You Should Know
- UsingFacebook’s Mystifying Privacy Settings
- Account and Privacy Settings
- 5 Ways to Protect Your LinkedIn Account
- 6 Security and Privacy Tips to Help You Deal With LinkedIn’s Current Security Crisis
Always have alternative email addresses
The selling of email addresses and personal data is rampant online, not to mention very easy to look up. Apart from that hacking cases also lead to the exposure of user data pertaining to online accounts. Here is where having alternate emails can be of use.
15 Websites to Send Anonymous Emails
Why go for anonymous email when there are plenty of premium featured and free email services such as... Read more
Using just one email everywhere may allow malicious people to get hold of and target the email for spam or identity theft. It’s a good idea to have an alternative email, for sending mail to strangers, signing up for newsletters or to filling up forms at unknown or untrusted websites.
This second email gets all the inevitable spam or unwanted emails while the official email remains clean and unexposed. Additionally, you can always forward important emails from the second address to your primary email and set a filter to keep those mail in a separate folder.
Simply add the second email to the first email’s account (using SMTP) and send mail as the second email directly from your official email only. This way your primary email account is nicely organized, free from spam, and even you don’t need to login to another account to do less secure tasks.
For creating a side or temporary email account, you can always use one of the popular email providers or go for a temporary/anonymous email provider:
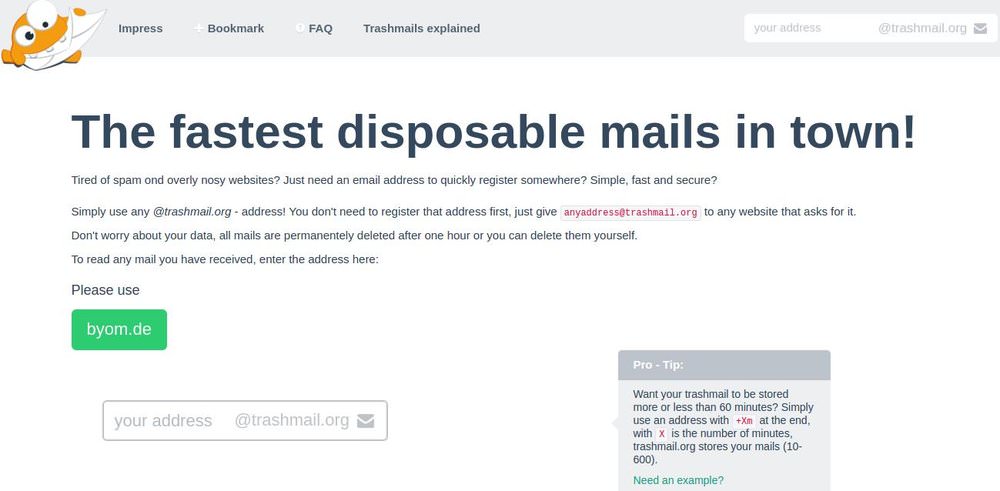
- Zoho Mail – One of the leading email providers wherein you can create a separate account for third-party emailing.
- Trashmail – A super-easy temporary email provider that doesn’t ask you to register an address – you just need to use it.
15 Websites to Send Anonymous Emails
Why go for anonymous email when there are plenty of premium featured and free email services such as... Read more
Also included are tips and tutorials for managing your mailbox with multiple email ids in a single inbox for popular email providers:
- How to forward emails in Gmail, Outlook and Yahoo Mail
- How to use/configure filters in Gmail, Outlook and Yahoo Mail
- How to send mails from different or secondary email address or using an alias in Gmail, Outlook and Yahoo Mail
Avoid logging into personal accounts at the workplace
Keeping business and leisure separate is always a good idea, especially when it is to do with personal accounts at the workplace. Avoid using your personal email address at work and never access private accounts like your bank account while at work.
If you’re really required to access your personal accounts for any reason, then do remember to do a security check using an anti-malware app. (Check out Malwarebytes).
Moreover, if you’re the owner or admin of your system and look for any suspicious program (though it’s hard to easily find a tracking software as it’s mostly hidden).
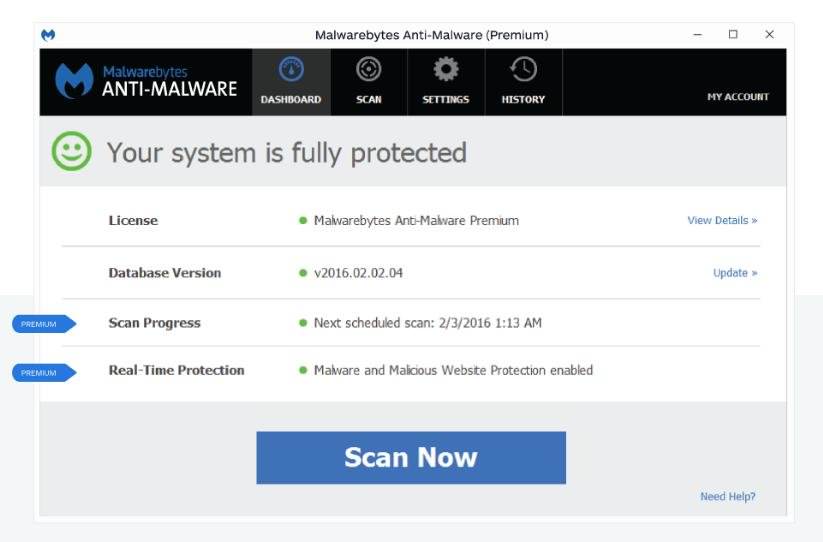
As an alternative solution, you can always use your smartphone coupled with data pack to send personal emails without getting tracked anyhow by your employer.
If you’re using the same on your employer’s WiFi, then do consider using Tor or a VPN (discussed below) or encrypting the mail contents for safety (discussed below too).
Enable two-factor authentication
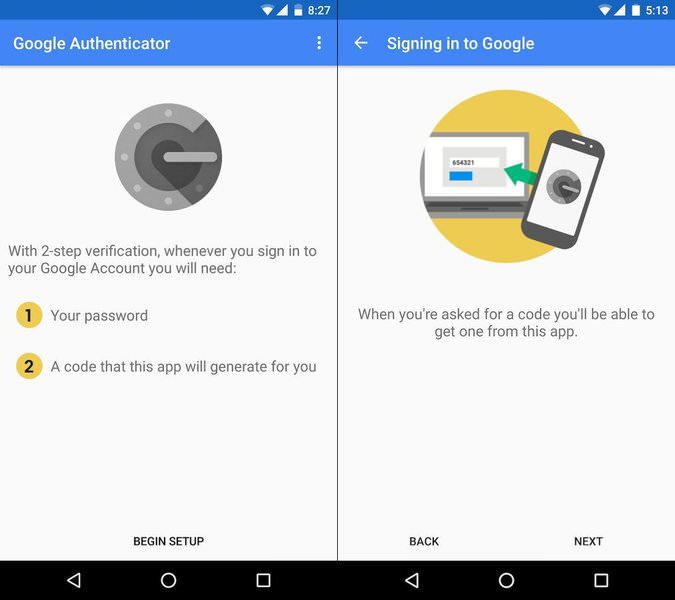
Two-factor authentication is a security mechanism that asks for a second key or passphrase in addition to the password. The same has been long used by high security systems (in the form of RSA hard tokens), but it is now generated and sent through text or email or generated using a smart app.
Two-factor authentication keeps away snoopers from accessing your online accounts – even if they get their hands on your passwords somehow. Here are some notable 2FA apps you should be using:
Use Tor or a VPN service

Tor is an online traffic router and encryptor, letting everyone believe you’re using the web from a different location and encrypting your traffic to safeguard against prying eyes.
A VPN is a traffic encryptor for disguising and securing your web data to avoid tracking and censorship from hackers, employers, ISPs and governments.
Using Tor or a VPN prevents third parties from monitoring your activities and keeps you safe from various types of hacks and attacks. Both technologies route your web sessions inside encrypted tunnels to safeguard your privacy.
10 Best VPN Service Providers
Everything is being tracked nowadays, from your activities on the internet to your phone and computer. Each click,... Read more
One can think of this tunnel as a private, self-owned phone wire between you and Tor network or the VPN provider. This guarantees that no other person can check or track your online activities or look into your data.
Check below for how to download and setup Tor or the popular VPNs easily:
- Tor – Peer-to-peer, free traffic router for and by privacy enthusiasts (Download | How to install)
- CyberGhost – Popular and free VPN service known and trusted for its quality (Download | How to install)
15 Best Free VPN Services to Protect Your Online Privacy
Discover our curated list of free VPN tools based on in-depth research. Read more
Encrypt everything

Encryption packages the private data including passwords, financials, images and videos inside password-protected containers that works like ‘a box with a lock‘. That locked box can be opened only by you and other authorized parties (having password). This will help you keep your communications private and hence avoid various types of attacks or thefts.
Read Also: 10 Online Storage Solutions with Encryption
Check below some of the tools that help encrypt your emails, IMs, online documents, data on cloud storages, etc.:
- Tutanota – Inspired by the FOSS principle, it offers a completely free, encrypted email service out of the box.
- Hushmail – Provides enhanced security features to keep your emails safe and protected (including attachments).
- ChatCrypt – Encrypts your messages, making them readable only by the participants having the same secret password.
- Cyph – A free in-browser messenger app with built-in end-to-end encryption for having private, encrypted conversations.
- DocSecrets – An add-on for Google Docs that encrypts sensitive information (like passwords) and highlights the secret texts.
- Cryptomator – A free client-side encryption tool to encrypt your files before sending or storing them at any online cloud storage.
- SecureGmail – A free tool from Streak to send encrypted mails using your favorite Gmail (receiver is asked for password to read).
- Mailvelope – An open source mail encryption tool that works for Gmail, Outlook, Yahoo Mail and few others.
10 Best Google Gmail Alternatives
Gmail is a popular email service provider used by millions, however there are many features that it misses... Read more
More apps:
- Ghostery – Protects you from the unknown trackers and gives you the power to manage your personal data.
- Disconnect – Supports private browsing and searching, and prevents malware and adware from websites to track your activities.
- Adblock Plus – Blocks various trackers, annoying ads, compromised domains, pop-ups as well as video ads while surfing the web.
- Privacy Badger – Blocks the spying ads and invisible trackers from monitoring your online actions (and comes from EFF).
Use Ad-blocker plugins

Tracking-blocker plugins are browser extensions that help you get rid of online trackers, ad agencies and other organizations that tracks and feeds on your data. Such trackers keep record of everything you do online (which websites you visit, what searches you make, which ads you click, etc.).
Using tracking-blocker or ad-blocker plugins in your browser lets you browse the web privately with no one monitoring your online activities for monetary profits. It also minimizes page-loading time and saves your Internet bandwidth (by small ratio, though).
Find below the links to download and set up such cross-browser, cross-platform plugins:
Understand browser cookies
Most of the sites install cookies in your browser, which are used for tracking your session data and user’s login information as long as you’re browsing the same website.
Some cookies are also used for cross-site tracking, to serve adware and show irritating pop-ups. Hackers can, unfortunately, hijack these to gain access to your logged-in accounts.
Install cookie management tools
To prevent cookies from tracking your data or revealing important information, you need to manage cookies using cookie management tools.
Such tools give you total control over cookies in the browser – view, manage or clear/delete them. By storing the right cookies and deleting all suspicious or sensitive cookies (that holds login or account info), you can be sure they won’t compromise security of your data or logged-in accounts.
- Cookie Manager – A Google Chrome add-on that lets you add, edit and delete cookies through the toolbar.
- Firebug – A Firefox add-on that manages cookies in your browser and helps filter and delete them easily.
- IECookiesView – A third-party tool that details all cookies in the Internet Explorer and assists you in managing them.

Did you find it helpful to secure your online experience? Do you know any more tips? Please share your knowledge and experience with us through comments section below.