Protect Your System from Internet Threats Now!
You probably have not heard of DNSChanger malware. If this is true, you have probably less than 48 hours to know what it’s about and how it could affect you. Come to think of it, we know what it could do to you: it could keep you off the Internet from the 9th of July onwards. You will experience firsthand what the death of the Internet feels like.
We hope we got your attention already because time is of the essence. Let’s cover the basics real quick.
Understanding DNSChanger Malware
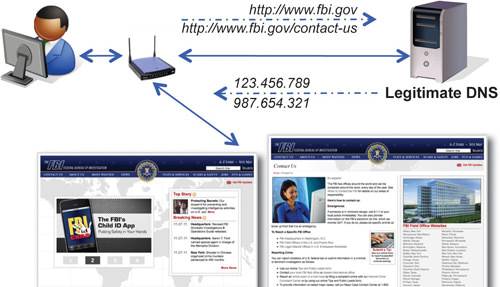
DNSChanger is malware discovered in 2007 that infected millions of computer systems worldwide. Cybercriminals released it to take control of your web server. The malware intercepts websites visited by your web browser and redirects you to other sites they prepared, so you will then use the server under their control. Once you are infected, you are set to use only their server every time you go online. This DNS server will alter every user search, giving fake and malicious answers as well as promoting fake and dangerous products. It is showing users an altered version of the Internet.

The main idea of this server is to easily push web ads to you, earning themselves millions of dollars. You can still surf the Internet like normal if the server keeps running.
Why You Should Remove DNSChanger Malware
When the FBI and the Estonian Police seized these controlled servers sometime in 2011, they cleaned up all the crime operations. However, the servers were kept running to serve all infected systems. If they had shut the server down, the web activities of these infected systems would be disrupted. This means that if your system is one of the infected ones, you can no longer go online.
Since the seizure, a special group called DNSChanger Working Group (DCWG) was assigned to maintain the servers, but as it was a costly operation to maintain, a final decision was made to turn these DNS servers off.
This will happen on July 9th, 2012.
Earlier this year, there were about 450,000 computer systems still infected, but it has now been reduced to about 277,000. With the downtime on these servers, if your system is among the 277,000 infected, you will not be able to go online after July 9th – unless you remember every IP address of the websites you want to visit.
How to Find Out if Your System is Infected
Firstly, you must find out if your system is among the still affected 277,000 systems. Since May 2012, Google has taken the initiative to inform you if they found the DNSChanger Malware in your system, by giving you an alert on their website. When you see the alert, click on the link ‘Learn how to remove this software’ and Google will guide you on the steps to remove the malware.

If you don’t see the warning on Google’s site, you can also visit DCWG’s official website to find out if your system is one of the victims, and if it is, follow the guide to removing it.
How to Remove DNSChanger Malware
If you have been affected by the DNSChanger Malware, you need to fix your computer system. Researchers suggest that the only way to fix your computer is to reformat your hard drive and reinstall the Operating System from scratch. Reverting your OS to a prior backup is not enough since the malware will be able to reclaim your system.

As suggested by DCWG, there are a few steps to follow if you are infected:
-
Backup all your important files.
- Follow the self-help guide as provided by the ‘free tools’ in the list below.
-
Once your computer is clean, follow instructions to ensure your DNS settings are correct.
- After fixing your computer, make sure your router (if you are using one) uses the DNS settings provided by your ISP.
- Changing DNS is only one of the functions of the malware kit. The malware could have captured some of your important information, so it is a good idea to check your bank statements and credit reports and take precautions by changing your passwords on any online accounts.
There are several free tools with self-help guides available to help you remove DNSChanger and related threats:
- Hitman Pro (32bit and 64 bit versions)
- Kaspersky Labs TDSSKiller
- McAfee Stinger
- Microsoft Windows Defender Offline
- Microsoft Safety Scanner
- Norton Power Eraser
- Trend Micro Housecall
- MacScan
- Avira
How to Protect Yourself
To learn how to protect yourself from malware infections, check out the following web references which guide you in protecting yourself from DNSChanger and many other malware: