Heartbleed: What Is It And What Should You do About It?
If you see a red, hollow, dripping heart symbol in your news feed, then yes, you’ve probably heard of the latest security breach to hit the Internet: Heartbleed. The security bug that’s compromised the security of accounts on sites like Yahoo, Facebook and even the Canadian Revenue agency has the whole Internet is up in arms. You’ve probably been asked to change your passwords for your emails, online accounts etc, but hold up.
In the midst of all this information, though, it’s can be hard to make heads or tails of what’s going on exactly. What is Heartbleed, exactly? Is it really as dangerous as everyone’s saying? How can you find out if you’re affected? Here’s a quick look at some of the main issues surrounding Heartbleed and what you can do about it.
Recommended Reading: The State Of IT Security [Infographic]
What Is Heartbleed?
Heartbleed is a bug that affects the OpenSSL service, which is a cryptographic library that’s used to encrypt data on more than two-thirds of all the websites on the Internet. If you’ve ever seen that locked padlock logo in your browser, or visited a site using the https: protocol, then you’re familiar with OpenSSL.

The Heartbleed bug exposes data held in a server’s RAM, meaning just about anyone has access to, and can snoop on Internet traffic, even when it’s supposedly encrypted.
Interlopers, if any, could take advantage of Heartbleed to obtain the keys and data that they’d need to decipher and read all the encrypted data that recently passed through a server.
Is It A Problem?
Given the fact that more than two-thirds of websites and services on the internet use OpenSSL, yes, Heartbleed is quite a major problem. However, it’s important to bear in mind that Heartbleed is not malware or a virus, and thus, a site affected by Heartbleed may not necessarily have had any data stolen. And it’s been around, undetected, since 2012.
Pretty much all forms of personal, encrypted information are vulnerable to Heartbleed. As long as it passes through the OpenSSL protocol, someone could have accessed it illegitimately. Passwords, emails, user names, communications — you name it, it’s probably accessible in some form or another due to Heartbleed.
So, yes, it is a problem.
How To Tell If You’re Affected
While it’s true that not every service has been affected by Heartbleed, it’s still better to be safe than sorry. While you can’t know for sure whether your own data has been compromised, there are a couple of services out there that can help you check whether you’re affected by Heartbleed.
Filippo Heartbleed Test
This Heartbleed test sends out malformed heartbeats to the website of your choice, extracting around 80 bytes of memory as proof. In other words, the test attacks the site much like a hacker would, to test whether the site is vulnerable to Heartbleed.

Heartbleed Checker
Here is a tool for you to check for affected sites. All you have to do is to type in the domain of the website you want to check and then click on See if the site is vulnerable to Heartbleed.

What To Do If You’re affected
If from the checks, you’ve found that you have an account on a site that could be compromised by Heartbleed, you have to decide on a course of action. The common wisdom is to immediately change your password, but this advice ignores one crucial fact: there’s no point changing passwords if the site hasn’t been fixed.
Heartbleed, as discussed earlier, isn’t a simple database leak, so simply changing your passwords won’t help if the problem hasn’t been fixed by the site. Some websites and services, such as Google, will have made this clear, but there will definitely be websites that don’t explicitly state whether they’ve rectified the issue on their end.

What you can do now is to use either of the two tools listed above, or check the site to at the Mashable lists to see if the service is still vulnerable.
Note that the two tools and the GitHub list don’t differentiate between services that were never vulnerable and services that have been fixed. It’s probably safer that you change your passwords if the site reports as not vulnerable.
Simply taking a break from affected services might help too, since Heartbleed only exposes data that’s in a server’s RAM.
Password Security
While Heartbleed goes beyond just an issue with password security, it’s still a good time to remind ourselves of some of the best ways to ensure the security of online accounts. Yes, there’s more to password security than just changing your password every few months.
Read Also: Golden Rule To Internet Security: Change Your Passwords
While two-factor authentication may not necessarily protect you from Heartbleed, it’s still a great security measure that you should definitely take advantage of on any services that support it.

If you’re unfamiliar, two-factor authentification is a way of verifying the identity of a user based on two steps instead of one. In other words, instead of just asking for a username and password, two-factor authentification also requires you to key in a verification code or use a smartphone app to further verify your identity.
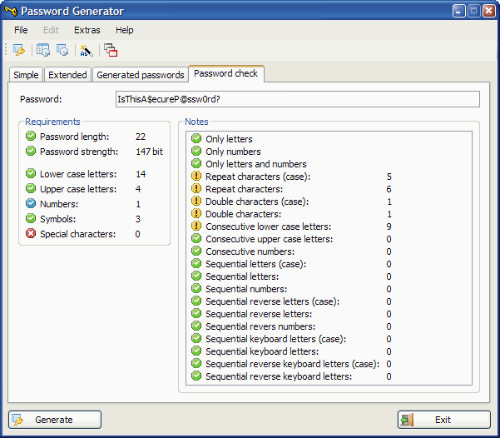
Another security measure you should probably take is to use tools to generate and manage passwords for you. The major benefit of these tools is the fact that they will create randomized passwords and manage them for you; no more having to memorize a ton of different passwords or, even worse, use the same password on multiple websites.
Read Also: 20 Desktop Tools To Generate And Manage Passwords
Conclusion
Heartbleed is a serious security issue that affects almost everyone on the Internet, and there isn’t much that any of us can do about it. Beyond checking the services we use and changing our passwords if they’ve fixed the flaw, or taking a break and remaining vigilant if they haven’t, it’s really all in the hands of the server administrators. If anything, Heartbleed serves as a reminder that we can never take the security of our personal data for granted.