A Guide to Understanding and Managing Android App Permissions
Smartphone apps have become an integral part of our daily lives. While Apple’s App Store has strict guidelines for app approval, Google’s Play Store is comparatively more relaxed. As an Android app user, it’s crucial to know what kind of data your apps are collecting from you.
Moreover, it’s important to be informed about the “permissions” you grant to the apps you install. Failing to do so could expose you to significant privacy and security risks.
This guide aims to shed light on the app permissions you should scrutinize. We’ll also discuss which permissions are legitimate and necessary for apps to function properly.
By being vigilant and understanding how to manage your app permissions effectively, you can reduce risks. Let’s delve into the world of Android app permissions and how to navigate it wisely.
How to Tighten Security on Android Device
Simple strategies you can follow to keep your Android phone or tablet secure from malware and vulnerabilities. Read more
Understanding the Nature of App Permissions
Let’s start by clarifying a common misconception: Android app permissions are not optional requests; they are mandatory requirements. Unless you have a rooted device, you don’t have a choice – other than opting not to install the app – regarding whether the app will obtain all the permissions it needs.
When you download an app from the Play Store, a pop-up appears, listing all the permissions the app needs. These can range from access to your storage and phone calls to network communication. It’s crucial to read this list carefully.
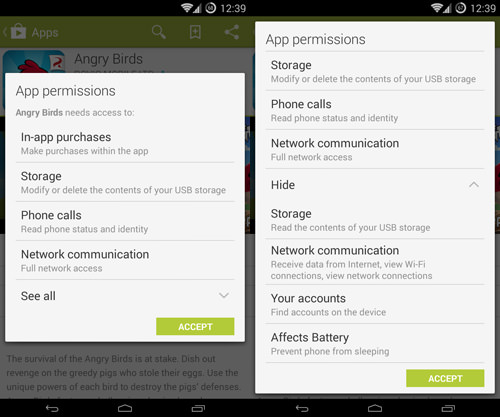
While it may be tempting to gloss over the permissions list as if it were an EULA (End User License Agreement), which most people don’t read, doing so could be risky. The difference could be between keeping your data secure on your device and making it accessible to dishonest app developers.
Five App Permissions to Approach with Caution
There are certain permissions that warrant extra caution. Not because they’re inherently harmful, but because the consequences could be severe if this data falls into the wrong hands. Keep in mind that these aren’t the only permissions to be cautious about – consider this a starting point.
For a more comprehensive understanding, you can refer to the discussion and list by AndroidForums.com user Alostpacket, as well as the official list of permissions on the Android Developers page. This article summarizes information from both sources.
1. Location Permissions
Android apps can request two types of location permissions: “approximate location (network-based)” and “precise location (GPS and network-based)”.
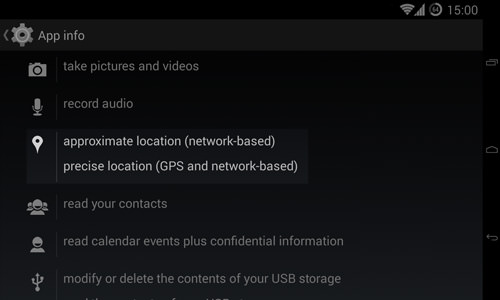
Why would apps need your exact location? Navigation apps like Waze need this data to function. Social media platforms may also use your location for posts and photos. Additionally, apps with location-based advertising will require this information. It’s a trade-off when using free, ad-supported apps.
2. Phone Status and Identity
This permission, “read phone status and identity,” can be tricky. It covers a range of data, from incoming phone calls to your device’s IMEI number.
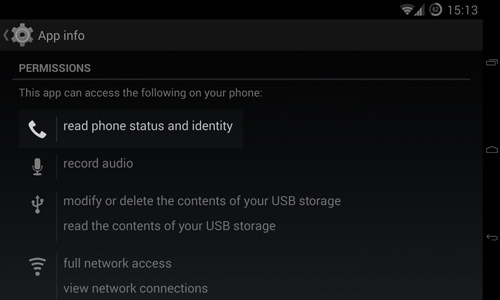
While generally safe, the potential for misuse is high. Exercise caution and think twice before granting this permission, especially if the app doesn’t seem to need it.
3. Access to Your Contacts
The permission to “Modify your contacts, read your contacts” gives apps unrestricted access to your contact data. The “modify” permission is particularly risky as it allows the app to read all your contact information.
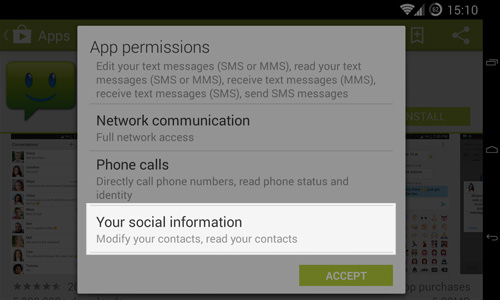
Some apps like SMS and contact management apps may require these permissions, but apps without a social component have no reason to request them.
4. SMS and MMS Permissions
These permissions can be costly if misused by malicious apps to send unauthorized messages or incur extra charges.
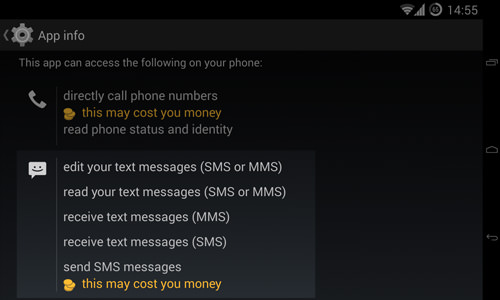
Permissions like “read your text messages” and “receive text messages” can also compromise your privacy. Be cautious and avoid apps that don’t have a valid reason for requiring these permissions.
5. Account-Related Permissions
The “Find accounts on the device” permission allows the app to check for accounts on services like Google and Facebook. The “Use accounts on the device” permission lets the app use these accounts without asking again, which could be risky if the app has malicious intentions.

Another permission to be cautious of is “create accounts and set passwords”, which can be exploited by malicious apps for phishing.
Strategies for Enhanced App Security
Ensuring app security involves a few proactive steps:
1. Instead of outright avoiding apps with questionable permissions, assess the app itself. Use reasoning to determine if the app genuinely needs the permissions it requests.
2. Consider reaching out to the app developer via email to inquire about the permissions. If the response is unsatisfactory or absent, it’s wise to skip the app.
3. Leverage the extensive Android community for insights. Read Play Store reviews and consult forums and Android-focused news sites for any recent complaints about the app. A bit of research can go a long way in ensuring your security.
How to Keep Your Smartphone Secure (6 Vital Tips)
Certain precautions to help you secure your smartphone and its data. Read more
How to Manage Your App Permissions
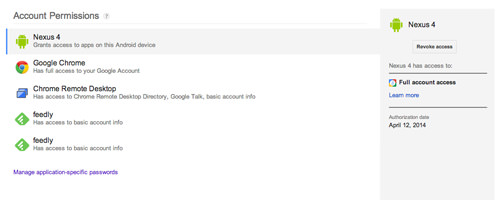
If you’ve granted apps access to accounts like Facebook or Google, it’s advisable to visit your account settings to manage these permissions, if such an option is available.
You can also review the permissions of individual apps by navigating to Settings > Apps. Select an app and scroll down to view its permissions.
10 Must-Know Google Settings for Android Users
If you're an Android user, you're probably aware of how important Google is to the operating system. From... Read more
Using Permission Management Apps
Apps like Permission Explorer can help you get a more detailed overview of app permissions. They allow you to filter by categories, apps, and permissions. Other similar apps to consider are App Permissions and Permissions Manager.
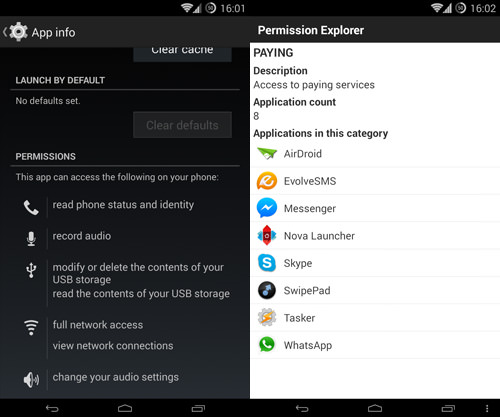
Regardless of the app you choose for this purpose, taking the time to review the permissions of your installed apps can help you identify any that may require attention or even removal.
How to Revoke App Permissions
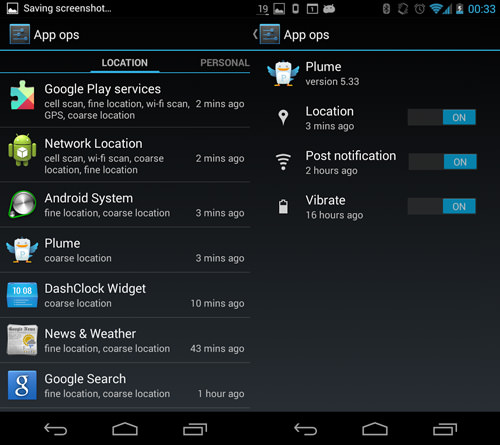
If you’ve identified apps with questionable permissions, the next step is to decide what to do. Unfortunately, the latest Android versions don’t offer a built-in feature for managing app permissions, as Google removed the AppOps feature starting from Android 4.4.2.
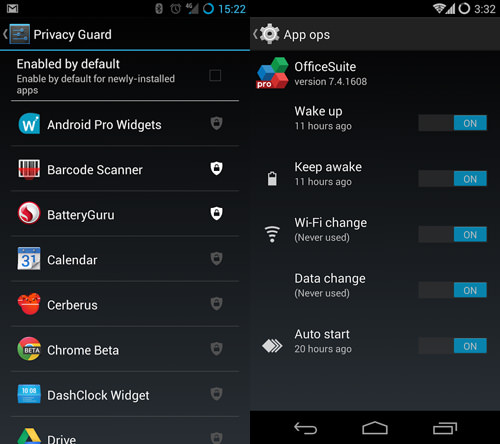
If you’re using Android 4.3, you might find AppOps useful for accessing the built-in permissions manager.
For those on stock, unrooted Android 4.4.2 or earlier versions, your options are limited. You can’t revoke app permissions unless you uninstall the app. However, if your device is rooted, you have more choices.
Permission Management Apps for Rooted Devices
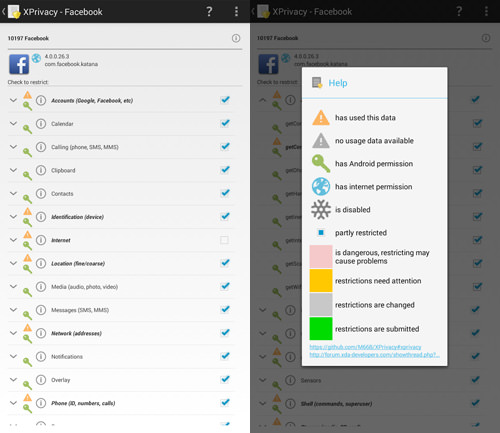
If you’ve installed the Xposed Framework, you can try XPrivacy. It’s one of the most comprehensive permission management apps, allowing you to modify, block, or revoke nearly all permissions. The XPrivacy Installer can assist with the installation.
If you’re open to installing a new ROM, some custom ROMs come with built-in permission management features. For instance, CyanogenMod has a Privacy Guard feature that integrates Android 4.3’s AppOps.
Final Thoughts
It’s evident that Android’s default privacy and security settings could be improved. From occasionally confusing permission names to the lack of selective permission granting, there’s room for Android to enhance its features.
Despite these challenges, you can still safeguard your data by being cautious about the apps you install and the permissions they request. After all, it’s your data and your device – you have control.