Android Exploit ‘Cloak & Dagger’ Can Steal Your Passwords
Android users may want to keep a close eye on the apps they download onto their devices as researchers have discovered a series of vulnerabilities in the operating system that relies on two particular Android permissions to work.
Dubbed Cloak & Dagger by the research team that discovered the vulnerability, the attack relies on abusing the SYSTEM_ALERT_WINDOW and BIND_ACCESSIBILITY_SERVICE permissions in order to compromise the system.

The way the exploit works is pretty straightforward: a malicious app gets downloaded and installed to the Android device, with the necessary permissions being granted without requiring the user’s input.
From there, hackers are able to perform clickjacking, record keystrokes, phishing, and even installing a God-mode app, all without the user being aware of it.
In order to illustrate the danger that the vulnerability poses, the researchers have prepared three videos that demonstrates the potential attacks that could be carried out.
The first one is called the Invisible Grid Attack, and it works by placing an invisible overlay over the device’s keyboard. With it, the hacker could identify the information that is being typed out.
The second video depicts a clickjacking attempt that eventually culminates in a God-mode application being silently installed in the background without the user even noticing it.
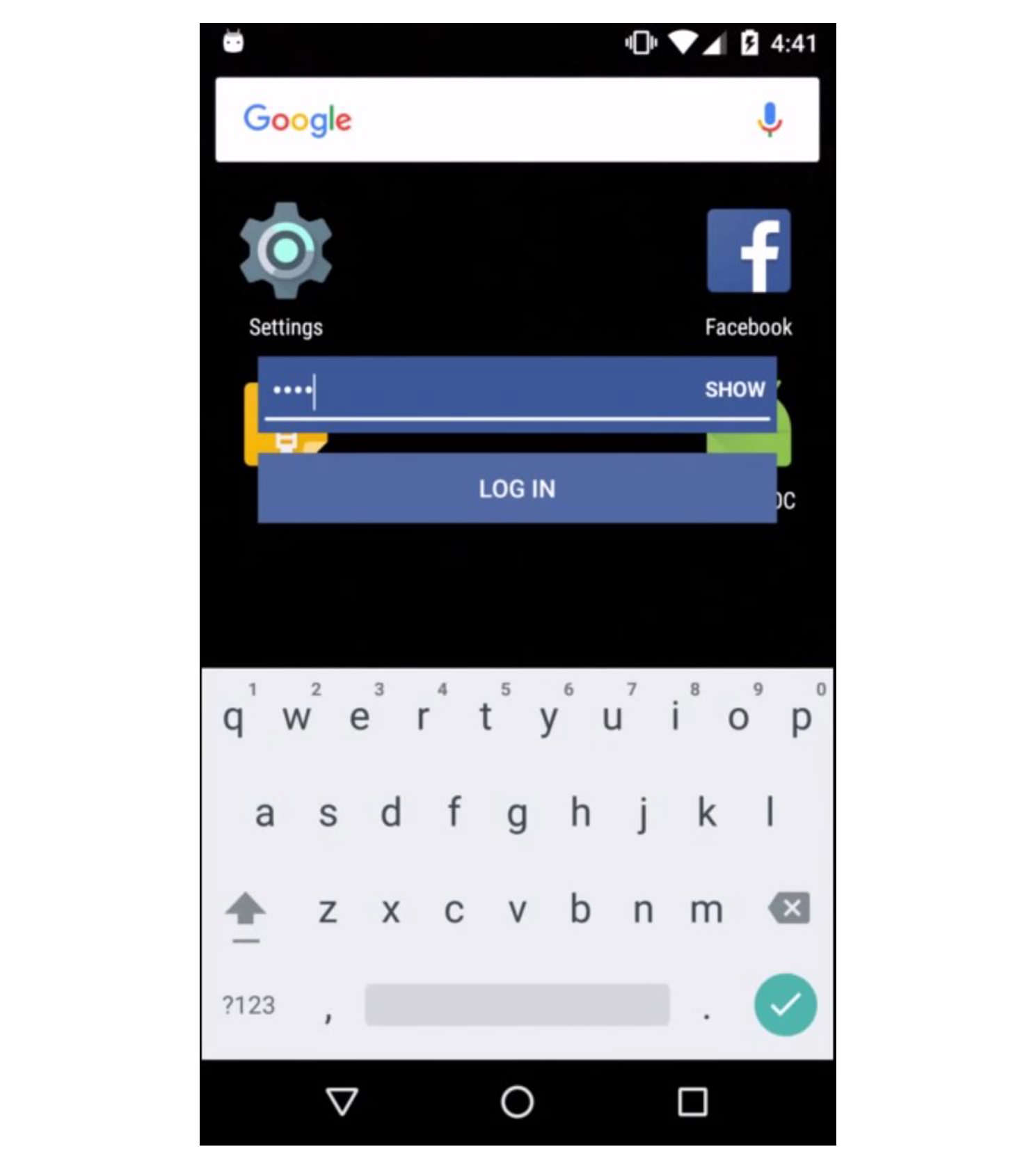
Finally, the third video showcases how a hacker could steal a password by manipulating the overlays.
So which version of Android is susceptible to this particular vulnerability. Unfortunately, the vulnerability is applicable across all Android versions, including the current version of Android 7.1.2 Nougat.
Not everything is doom and gloom however, as Google has since been notified of the vulnerability, so rest assured that the company will be looking for ways to fix it.
In the meantime though, do keep an eye on the apps that you download off the Google Play Store.
Read Also: How to Keep Your Smartphone Secure (6 Vital Tips)